
The IoTeX bridge incident reveals critical cross-chain security risks. Explore the exploit, and its implications for interoperability.
Author: Kritika Gupta
In the fast-evolving world of blockchain infrastructure, cross-chain bridges play a critical role in enabling interoperability between networks. However, they also represent one of the most vulnerable layers in decentralized finance. The IoTeX bridge incident, which occurred on February 21, 2026, exposed these structural risks once again. IoTeX, a Layer-1 blockchain designed to power machine economies, IoT devices, and real-world AI applications, suffered an exploit after an attacker compromised a validator owner’s private key on the Ethereum side of its ioTube bridge.
However, on February 21, 2026, IoTeX became the latest major project to face a bridge exploit. IoTeX operates as a Layer-1 blockchain specifically designed for IoT devices, machine economies, and AI-driven applications. An attacker compromised a validator owner’s private key on the Ethereum side of IoTeX’s ioTube bridge. Consequently, the attacker drained approximately $4.3 to $4.4 million in bridged assets. In addition, the attacker minted millions more in wrapped tokens, which independent estimates valued at significantly higher amounts.
Although IoTeX contained the exploit relatively quickly, the incident reignited concerns across the crypto ecosystem. Specifically, the exploit exposed persistent bridge security risks, private key management vulnerabilities, and recovery limitations in permissionless systems. Importantly, IoTeX confirmed that its Layer-1 blockchain remained secure. Therefore, the breach resulted from operational security failure rather than flaws in consensus or smart contract architecture.
Nevertheless, this incident reinforces a broader structural reality. Even technically sound blockchain systems can fail when human operational controls intersect with large concentrations of value. In response, IoTeX pledged full compensation to affected users. The team also deployed emergency upgrades, blacklisted malicious addresses, and offered a 10 percent white-hat bounty for fund recovery. Therefore, this event now serves both as a case study in rapid incident response and as a warning about bridge risk concentration. Notably, bridges have accounted for over $3 billion in losses since 2022.
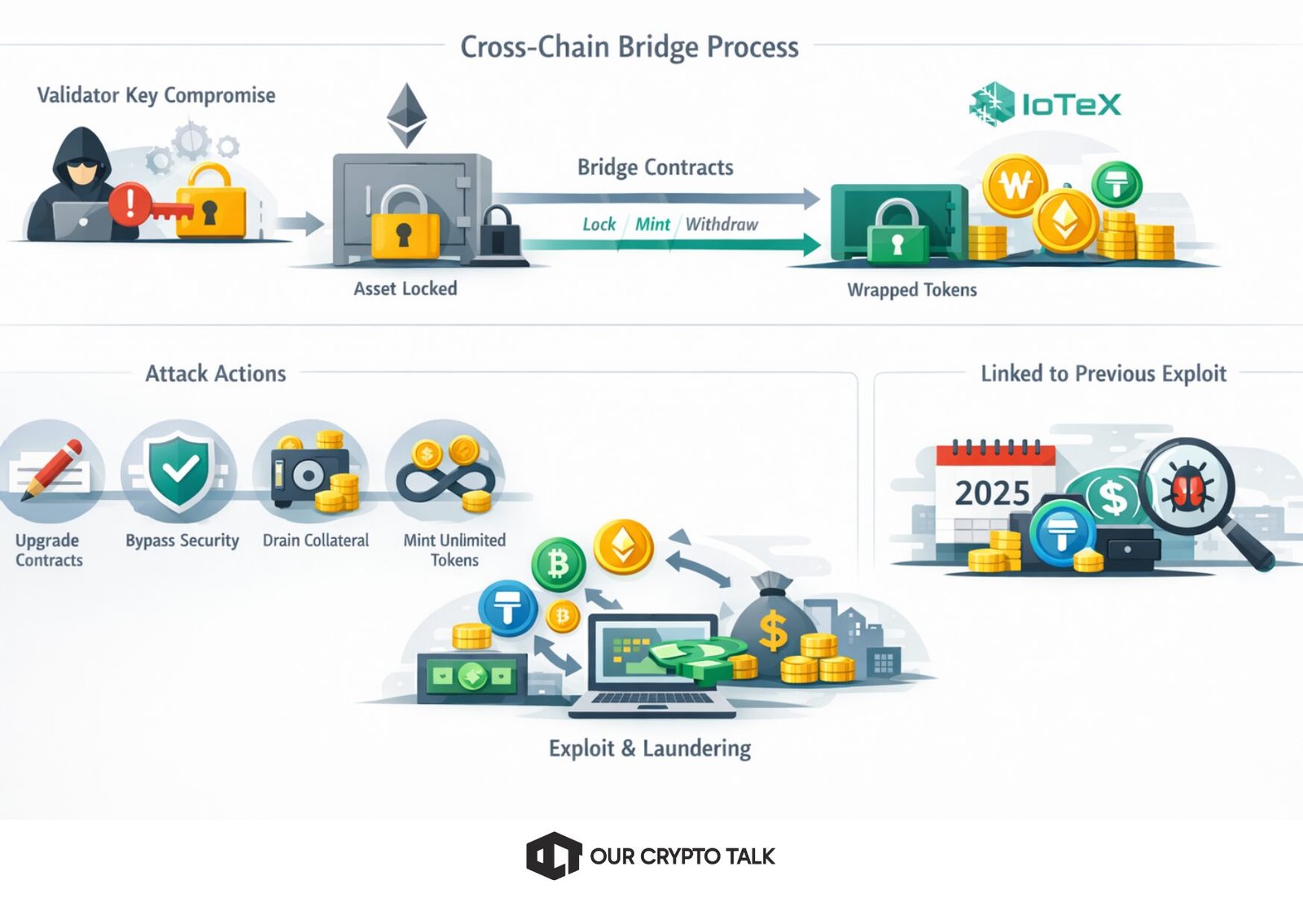
The IoTeX bridge incident resulted from a validator owner private key compromise, which remains one of the most dangerous operational risks in blockchain systems. Unlike smart contract exploits, this attack did not exploit faulty protocol logic. Instead, the attacker gained administrative control by accessing a privileged validator key.
The system relies on validator-controlled contracts, including TransferValidatorWithPayload, MintPool, and TokenSafe. These contracts perform core bridge operations such as asset locking, minting, and custody. Ideally, operators secure these contracts using multisignature wallets, hardware security modules, time locks, and key rotation procedures.
However, in this case, a single compromised validator private key allowed full administrative control. As a result, the attacker upgraded contracts, bypassed signature verification, withdrew real collateral, and minted unlimited wrapped tokens without backing.
Furthermore, on-chain evidence suggests that the attacker planned the exploit over an extended period. Analysts linked the attacker’s wallet activity to the February 2025 Infini stablecoin exploit. This connection indicates sophisticated operational capability and long-term preparation. The attacker executed 189 transactions within a narrow two-hour window. During this period, the attacker drained USDC, USDT, IOTX, WBTC, BUSD, and PAYG. Subsequently, the attacker swapped assets into ETH and routed approximately 66 BTC through laundering pathways.
Therefore, this incident highlights a systemic industry weakness. Bridges concentrate massive value into limited administrative control points. While audits can detect smart contract bugs, audits cannot prevent private key compromise through phishing, insider threats, or operational lapses.
IoTeX CEO Raullen Chai confirmed that the Layer-1 blockchain itself remained secure. Specifically, IoTeX’s Roll-DPoS consensus and native smart contracts showed no vulnerabilities. Instead, the breach remained isolated to Ethereum bridge infrastructure.Nevertheless, centralized control mechanisms within decentralized systems continue to attract sophisticated attackers. As DePIN and AI networks expand, attackers increasingly target infrastructure that connects real-world systems to blockchain environments.
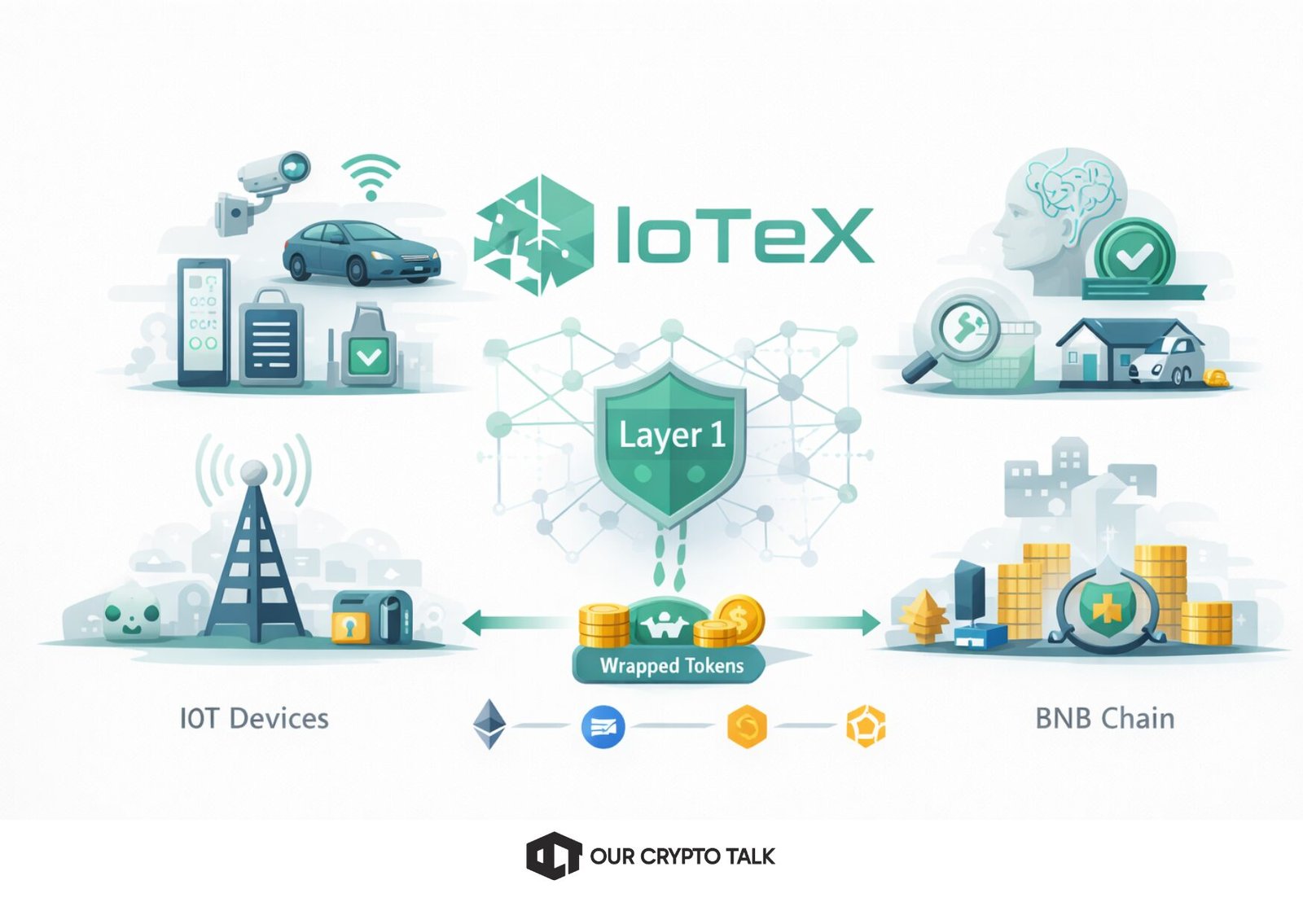
IoTeX launched in 2017 with a clear mission. The project aimed to create a blockchain capable of supporting machine-to-machine economies. Specifically, IoTeX focused on enabling IoT devices, sensors, and AI agents to interact securely and autonomously.
Unlike general-purpose blockchains, IoTeX optimized its architecture for real-world integration. Its Roll-DPoS consensus mechanism delivers high throughput, low latency, and efficient scalability. Consequently, the network supports machine-level interactions with minimal delay.
IoTeX positioned itself at the center of the emerging machine economy. The platform enables applications in decentralized wireless infrastructure, autonomous devices, AI data verification, and tokenized real-world assets.
The ioTube bridge played a critical role in this strategy. It enabled liquidity flow between IoTeX and major ecosystems such as Ethereum, Base, and BNB Chain. As a result, wrapped tokens allowed IoTeX assets to participate in broader DeFi ecosystems.
The IoTeX bridge incident did not compromise IoTeX’s Layer-1 blockchain. However, it exposed vulnerabilities within the bridge infrastructure that connects IoTeX to external ecosystems.
Key milestones related to the IoTeX ioTube bridge exploit and response
Attackers appear to gain access to the ioTube Ethereum-side validator owner private key during a long-dwell period of preparation.
The attacker uses owner-level control to drain bridged collateral and mint unbacked wrapped tokens through core validator and minting pathways.
On-chain analysts raise alerts and security firms confirm exploit activity, increasing visibility and accelerating response coordination.
The team and validator community halt bridge operations, isolate the issue to Ethereum-side infrastructure, and begin fund tracking and exchange coordination.
IoTeX issues an on-chain bounty message offering 10% for fund return within a fixed window, with escalation to law enforcement if ignored.
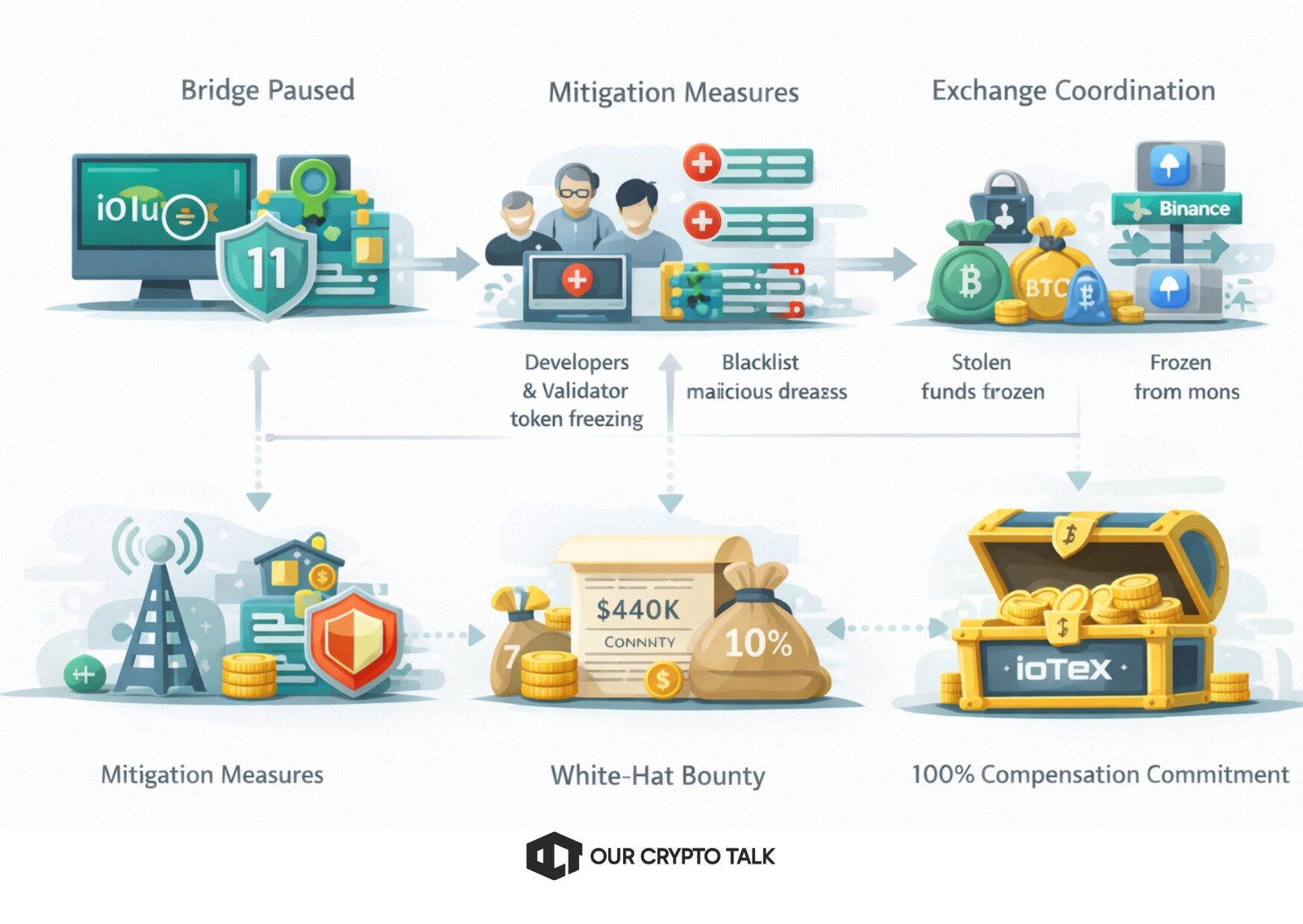
IoTeX responded quickly and decisively to the IoTeX bridge incident, which helped stabilize the ecosystem and protect users. First, the team immediately paused the ioTube bridge to prevent additional unauthorized transactions. Then, validators and core developers coordinated mitigation efforts and identified malicious addresses. IoTeX deployed a mainnet upgrade that enforced automatic blacklist protections, which froze millions of maliciously minted tokens and prevented additional liquidation.
In parallel, IoTeX worked with centralized exchanges to track and freeze stolen funds wherever possible. The team also offered a 10 percent white-hat bounty to incentivize voluntary fund return, following industry precedent used in major exploit recoveries.
Most importantly, IoTeX pledged 100 percent compensation for affected users through its treasury. This decision demonstrated strong commitment to user protection and ecosystem stability. By combining rapid containment, technical upgrades, and financial guarantees, IoTeX successfully stabilized the situation and reinforced long-term network trust.
<<-tweet-2025278610375143497->>
Loading chart...
The IoTeX bridge incident triggered immediate market volatility and investor uncertainty. Following disclosure, the IOTX token fell between 9 percent and 22 percent as traders reacted to security concerns and potential ecosystem risk. At the same time, trading volume surged sharply, reflecting panic selling, arbitrage activity, and short-term speculative positioning.
However, the decline remained relatively contained compared to historical bridge exploits. IoTeX’s rapid response, bridge shutdown, and full compensation pledge helped stabilize sentiment and prevent prolonged market damage. The successful freezing of most maliciously minted tokens also reduced inflationary pressure on circulating supply.
More broadly, the incident reinforced persistent investor caution toward bridge infrastructure. Bridge exploits continue to influence risk assessment, liquidity allocation, and institutional participation. Nevertheless, transparent crisis management and treasury-backed user protection helped restore partial confidence, demonstrating that strong operational response can significantly reduce long-term market impact and ecosystem erosion.
The IoTeX bridge incident highlights the urgent need for stronger operational security and infrastructure hardening. First, IoTeX must eliminate single points of failure by adopting Multi-Party Computation (MPC) or threshold signature schemes. MPC distributes key control across multiple independent parties, ensuring that no single compromised entity can authorize malicious transactions. This approach significantly reduces the risk associated with private key theft.
Second, IoTeX should integrate Hardware Security Modules (HSMs) for validator key storage. HSMs isolate private keys within tamper-resistant hardware, preventing extraction even if attackers compromise the surrounding software environment. This adds a critical hardware-level defense against remote key compromise.
Third, IoTeX should implement timelock mechanisms on bridge contract upgrades and administrative actions. Timelocks introduce mandatory waiting periods before critical changes execute. This delay allows monitoring systems and validators to detect and respond to suspicious activity before attackers can complete malicious operations.
Additionally, IoTeX should enforce rate limits on minting and withdrawal functions. Rate limiting restricts how much value can move within a defined timeframe, which limits exploit scale and gives defenders more time to respond.
Real-time anomaly detection systems must also monitor validator behavior continuously. Automated alerts for abnormal minting patterns, unusual transaction volume, or administrative changes can enable rapid intervention.
Finally, IoTeX should transition toward trust-minimized bridge architecture using cryptographic verification methods such as light clients or zero-knowledge proofs. These systems reduce reliance on privileged validators and replace trust assumptions with mathematical verification.
By implementing distributed key custody, hardware protection, delayed execution safeguards, and cryptographic bridge verification, IoTeX can significantly strengthen its infrastructure and reduce the likelihood of future exploits.
Bridge infrastructure introduces structural risks that extend beyond individual exploits. First, private key compromise remains a critical vulnerability. Attackers increasingly target operational access rather than smart contract logic because human-controlled keys create exploitable entry points. Second, bridges concentrate massive liquidity, often holding tens or hundreds of millions in collateral. This concentration creates high-value targets and amplifies exploit impact.
Third, unbacked token minting can disrupt DeFi markets by inflating supply and destabilizing collateral systems. Fourth, recovery remains extremely difficult once attackers convert assets through decentralized swaps or cross-chain routing. Fifth, treasury-funded compensation protects users but shifts financial burden to the protocol, potentially weakening long-term sustainability.
Finally, emergency actions such as blacklisting highlight decentralization trade-offs. These risks demonstrate that bridge security depends not only on code integrity but also on operational discipline, custody design, and infrastructure resilience.
The IoTeX bridge incident exposed operational security weaknesses. However, the incident also demonstrated effective incident response.IoTeX successfully contained damage, protected most assets, and committed to full user compensation.
Nevertheless, the event reinforces critical lessons. Bridges introduce systemic risk. Private key security remains essential. Recovery remains difficult.As blockchain infrastructure expands into real-world AI and machine economies, security must evolve accordingly.Ultimately, projects that prioritize transparency, operational discipline, and trust-minimized architecture will define the future of blockchain infrastructure.


IoTeX rolls out a defensive upgrade that blacklists malicious addresses and freezes a large share of attacker-controlled token flows.
IoTeX prepares user-facing claim and reimbursement steps while continuing fund tracing, exchange coordination, and follow-up security hardening.