
Explore the biggest ZachXBT revelations, from DeFi scandals to Lazarus hacks, exposing millions in crypto fraud and insider abuse.
Author: Kritika Gupta
In crypto, the ledger never forgets, but people often hope you do. That gap between permanent data and short public attention creates the perfect environment for fraud, laundering, insider abuse, and coordinated social engineering. ZachXBT revelations emerged in that environment as an anonymous, independent on-chain investigator who consistently converts raw blockchain footprints into narratives the community can act on. He does not “hack” systems. Instead, he traces flows, clusters wallets, connects off-chain identities through open-source intelligence (OSINT), and publishes evidence in a way that forces accountability.
Since 2021, ZachXBT revelations have repeatedly shifted outcomes. In several cases, his work helped trigger law enforcement action, exchange freezes, and community-driven governance responses. In other cases, he simply forced an uncomfortable truth into the open: crypto does not remove trust, it often just relocates it to founders, multisigs, and internal dashboards. As a result, his threads became a practical early-warning system for traders, builders, and institutions.
ZachXBT’s value comes from one simple reality: blockchains are transparent, but understanding them takes work. Scammers rely on the fact that most users will not follow the money beyond the first hop. They also rely on social dynamics: founders cultivate trust through branding, influencers, and community hype, while criminals exploit urgency through airdrops, presales, and “limited time” links.
ZachXBT revelations flips that dynamic. He uses transaction-level evidence to show how scams actually move funds, where they cash out, and how they reuse infrastructure across multiple incidents. That approach matters because it protects market participants in three ways.
First, it reduces information asymmetry. In many scams, insiders already know the project lacks liquidity plans, has suspicious treasury flows, or shares wallets with prior rugs. When an investigator surfaces those connections, the broader market can price risk faster, instead of learning through losses.
Second, ZachXBT revelations frequently lead to real-world consequences. Authorities have opened investigations after several ZachXBT revelations, and in certain cases arrests followed. Therefore, these disclosures move beyond online drama.
Third, it upgrades community behavior. Over time, repeated exposures train users to watch for common patterns: treasury managers with hidden identities, Discord compromises, wallet drain approvals, direct-to-wallet presales, and internal tooling that over-collects user data. That education does not eliminate risk, but it raises the cost of running scams at scale.
With that foundation, the six cases below show how on-chain evidence, when combined with persistence, can change outcomes even in a system designed for permissionless participation.

The Wonderland Sifu revelation in January 2022 became one of the first moments when DeFi users collectively realized that “decentralized” does not automatically mean “trustless.” Wonderland ran on Avalanche and marketed itself as a high-yield protocol centered on the TIME token. It attracted a large community because it promised treasury-backed value and aggressive compounding returns that looked unbeatable during the bull market. At its peak, Wonderland reached billions in total value locked, and it functioned like many DeFi protocols of that era: users deposited assets, the protocol managed a treasury, and a small group of key contributors executed strategy. That structure created a hidden single point of failure. It also created a hidden single point of trust.
ZachXBT published evidence that Wonderland’s treasury manager, known publicly as Sifu, matched the identity of Michael Patryn, a figure tied to the QuadrigaCX exchange saga. That allegation mattered because the treasury manager sits at the center of capital allocation. In practice, a treasury manager influences where the assets go, how risk gets taken, and how quickly funds can move. Therefore, if a protocol gives a treasury manager meaningful control, then the protocol asks users to trust that person’s competence and integrity, even if the contracts run on-chain.
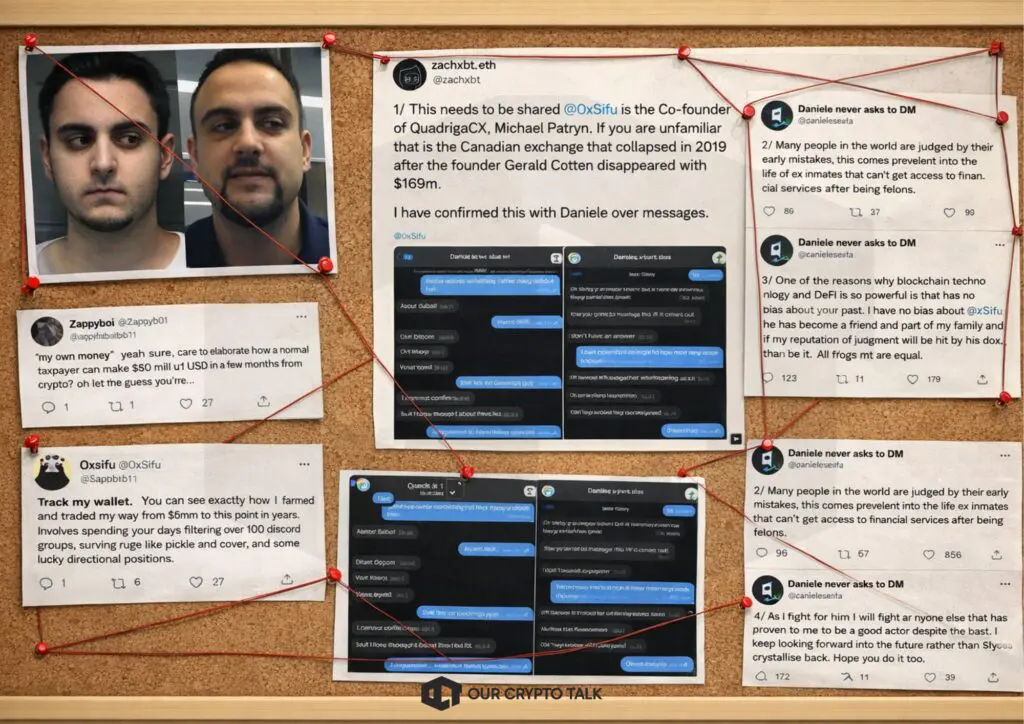
The QuadrigaCX connection amplified the shock. QuadrigaCX collapsed after its CEO Gerald Cotten reportedly died, leaving users unable to access funds. Later investigations described QuadrigaCX as fraudulent, with customer deposits used improperly. In that context, ZachXBT revelations did not simply introduce drama. Instead, it introduced an existential governance question: why did a DeFi protocol with a massive treasury allow a person allegedly linked to a notorious exchange failure to control that treasury under a pseudonym?
ZachXBT supported the claim through on-chain forensics and identity linkage. He used wallet tracing to show connections between addresses associated with Sifu and addresses historically tied to QuadrigaCX-related flows. He also referenced corroborating signals, including communications and admissions that circulated quickly after the thread. Once the allegation hit the market, TIME holders reacted immediately. First, they sold the token aggressively. Next, they withdrew deposits, which rapidly shrank TVL. Then, governance took over as the community demanded a decision about Sifu’s continued role.
The price action reflected a classic confidence collapse. TIME did not drop because an exploit drained the treasury at that moment. It dropped because users repriced the probability of future loss and mismanagement. In DeFi, that probability matters as much as current balances because treasury strategies, leverage, and liquidity management determine survivability. When trust breaks at the top, the market tends to assume the worst-case scenario, especially when treasury assets can move quickly and when communications get chaotic.
Responsibility focused on two main actors and one broader structural problem. First, it focused on Sifu if he concealed a past that would have materially changed how the community assessed risk. Second, it focused on Wonderland leadership because leadership decides who gets privileged roles and how much visibility the community receives about those roles. Third, it highlighted a systemic weakness in DeFi culture during that period: communities often treated pseudonymity as normal, while still handing enormous financial power to a small group. That combination created the conditions for reputation risk to become protocol risk.
ZachXBT revelations impact went beyond Wonderland itself. His work pushed DeFi users to ask harder questions about multisig signers, treasury controllers, and background checks. It also created pressure for protocols to improve transparency around who controls keys and how governance can remove them. After the revelation, Wonderland faced a governance crisis. The community debated removal, restructuring, or winding down. Even when a protocol survives such a scandal technically, it rarely survives it socially in the same form.
Ultimately, the Wonderland Sifu story became a cautionary case study: on-chain code cannot replace off-chain accountability when humans hold meaningful control. DeFi can remove some intermediaries, but it cannot remove the need for clear governance, controlled permissions, and explicit trust assumptions. ZachXBT’s investigation forced the industry to confront that reality early, and it set a standard for how on-chain evidence can expose the risks hidden behind a pseudonym.
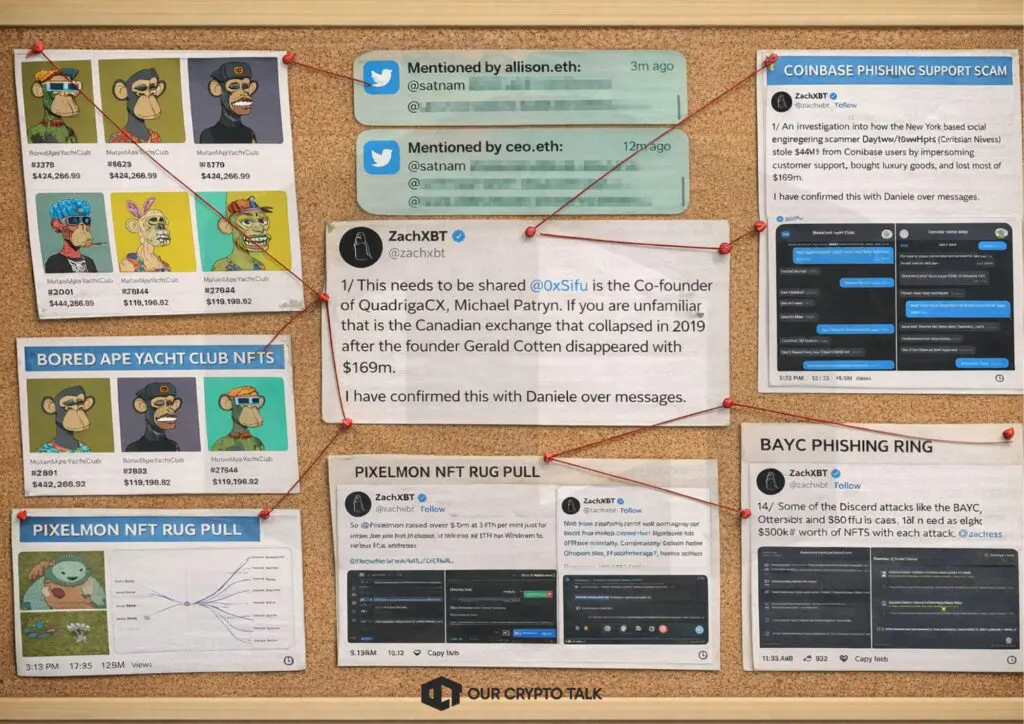
The BAYC phishing gang exposure showed how attackers can weaponize community trust faster than any smart contract exploit. During the 2021–2022 NFT boom, Bored Ape Yacht Club became one of the most valuable digital collectibles in the world. Buyers did not only purchase art. They purchased status, social access, and future airdrop expectations. That cultural premium pushed prices to extreme levels, and it also created a target list for criminals. When one NFT can sell for the price of a house, a phishing crew does not need to hack a protocol. Instead, it needs to trick a few holders into signing the wrong transaction.
The BAYC phishing gang exposure showed how attackers can weaponize community trust faster than any smart contract exploit. During the 2021–2022 NFT boom, Bored Ape Yacht Club became one of the most valuable digital collectibles in the world. Buyers did not only purchase art. They purchased status, social access, and future airdrop expectations. That cultural premium pushed prices to extreme levels, and it also created a target list for criminals. When one NFT can sell for the price of a house, a phishing crew does not need to hack a protocol. Instead, it needs to trick a few holders into signing the wrong transaction.
ZachXBT revelations showed a set of phishing attacks that targeted BAYC holders through the channels the community used daily, especially Discord and social media. Attackers relied on a simple, repeatable tactic. First, they compromised or impersonated trusted accounts, including verified Discord members or official-looking profiles. Next, they posted links that promised utility, early access, giveaways, or verification steps. Then, victims connected wallets and signed approvals. Finally, attackers drained NFTs and moved them quickly to marketplaces to sell for ETH. After that, they laundered proceeds through mixers and swapped through services designed to reduce traceability.
For a crypto reader, the key technical point is the signature model. In Web3, phishing often steals your authorization rather than your password. A malicious site can present a transaction that looks harmless and still grant blanket approval to transfer assets. Once the victim signs, the attacker does not need ongoing access. The approval itself becomes the door. That is why high-value NFT holders became vulnerable. They interacted frequently with links and mints, they kept assets in hot wallets, and they moved fast because they feared missing drops. Attackers exploited that urgency.
ZachXBT’s reporting connected the incidents into a broader network rather than isolated thefts. Wallet clustering to link stolen assets and proceeds to shared infrastructure were used.He correlated online handles, social profiles, and real-world identity signals with on-chain activity. This combination matters because a single stolen ape could look like a random crime. A clustered pattern reveals an organized crew. Once the pattern becomes visible, exchanges and marketplaces can identify cash-out routes, investigators can notify victims, and authorities can build cases.
The exposure also highlighted ecosystem weaknesses. Discord became a high-risk surface because communities treated it as semi-official infrastructure. Verification systems, bots, and role management created points of compromise. Meanwhile, NFT marketplaces enabled rapid liquidation of stolen assets, which converted unique NFTs into liquid ETH that criminals could move across rails. At the same time, many victims lacked permission hygiene. They did not revoke approvals after mints, and they used the same wallet for holding, trading, and community interactions.
Responsibility primarily rested with the phishing crew. They engineered the deception and ran the laundering pipeline. However, responsibility also spread to adjacent enablers. Influencers and community leaders sometimes amplified links without verification. Platform operators struggled to moderate fast-moving scam posts. Marketplaces and social platforms could not always react quickly enough to stop sales or flag obvious theft patterns. Still, the criminals drove the harm.
The financial damage became meaningful because of NFT prices at the time. Stolen apes, mutant apes, and associated assets often represented six-figure losses per victim. In aggregate, ZachXBT estimated multi-million dollar theft totals from linked incidents. Even when victims recovered some value later through seizures or legal action, most losses remained permanent because NFTs can change hands quickly and because laundering reduces recovery options.
ZachXBT revelations helped push real-world consequences. Public reporting around the case described legal action in France and indictments connected to NFT thefts valued in the millions. That outcome demonstrated a critical point for crypto security: criminals cannot rely on anonymity as a permanent shield if they reuse wallets, cash out through identifiable points, or expose themselves through social behavior.
The BAYC case also changed user behavior. Many high-value holders adopted a two-wallet system: one cold wallet for storage and one hot wallet for interactions. They began using transaction simulation tools and permission revokers. Communities improved verification practices and treated every link as hostile by default. That culture shift reduced the success rate of similar attacks over time.
In the end, the BAYC phishing gang exposure showed the human side of crypto crime. Attackers did not need advanced exploits. They needed social engineering, speed, and a permission model that rewards fast signing. ZachXBT revelations translated that messy reality into a traceable chain of evidence. He helped the community understand how the thefts connected, and he helped authorities treat them as a coordinated operation rather than random incidents.
ZachXBT’s Lazarus Group work matters because it operates at the highest level of adversary sophistication in crypto. Lazarus is widely described as a North Korean state-linked hacking organization that uses cyber theft to generate funds for the regime. Unlike opportunistic scammers who chase quick rugs, Lazarus runs long campaigns, adapts tactics, and treats crypto infrastructure as a strategic target. Therefore, when ZachXBT connects laundering clusters and overlaps across hacks, he does not only expose a crime. He helps the ecosystem understand how a nation-state actor behaves on-chain.
ZachXBT revelations repeatedly highlighted patterns that align with Lazarus operations: careful test transactions, rapid dispersal after theft, cross-chain bridging to complicate tracking, and systematic laundering through mixers and swap services. He also emphasized operational compromise, not just contract vulnerability. Lazarus often succeeds through social engineering, credential theft, compromised machines, and insider-level access. That approach changes the risk model for exchanges and protocols. An audit cannot stop a compromised signer. A secure contract cannot prevent an employee from approving a malicious transfer if the attacker controls the employee’s environment.
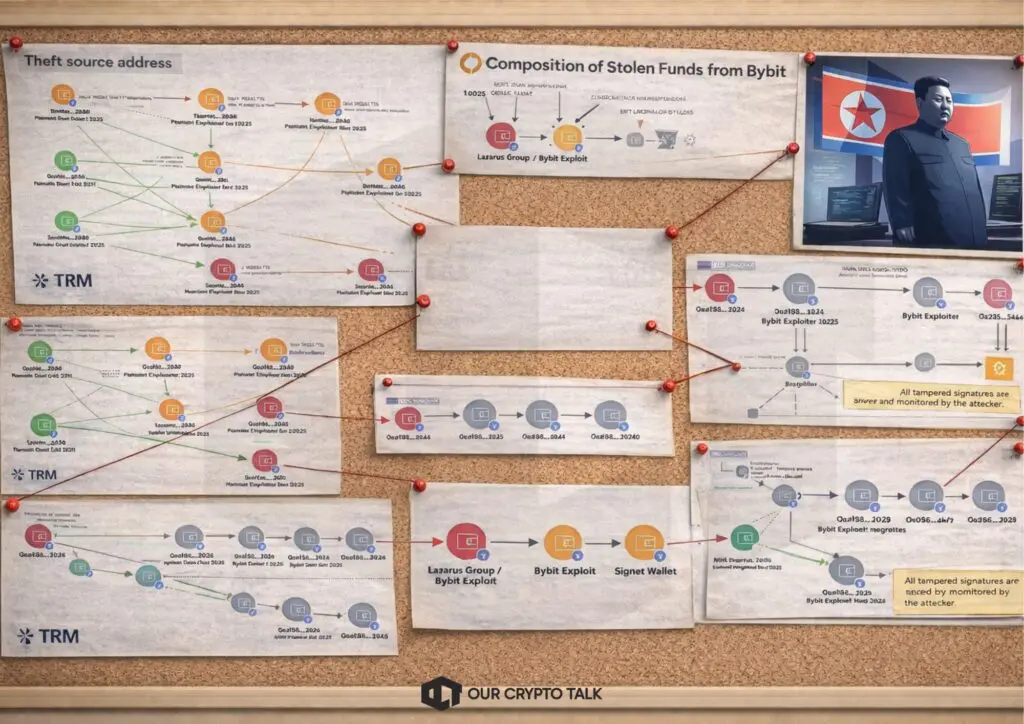
The most important contribution in these cases is linkage. Many hacks initially look unrelated. Different chains, different assets, and different victims create noise. However, state-backed operators reuse infrastructure over time because they optimize processes. They reuse wallet patterns, laundering routes, timing behaviors, and sometimes even specific addresses. When ZachXBT revelations and other investigators identify overlaps, they strengthen attribution confidence. That confidence then helps exchanges, compliance teams, and authorities coordinate faster responses.
For crypto readers, the operational lesson sits in the laundering pipeline. Lazarus does not only steal. It must also convert stolen assets into usable value. That conversion creates chokepoints. Mixers, bridges, OTC brokers, and non-KYC exchanges can facilitate laundering. At the same time, they create observable behavior, such as repeated deposit sizes, timing cycles, and chain-hopping patterns. When investigators map these patterns, they can alert infrastructure providers and reduce the attacker’s ability to cash out at scale.
ZachXBT revelations also highlighted infiltration risks through fake identities and outsourced hiring channels. When attackers place operatives inside crypto companies, they can obtain privileged access to internal systems, key management workflows, or security processes. That is why his commentary often moved beyond “here is the thief wallet” and into “here is how the attacker enters the organization.” In practical terms, that means projects must treat security as both technical and organizational. They need strict access controls, role-based permissions, continuous monitoring, and multi-person policy for large transfers. They also need hiring diligence, device security, and compartmentalization of credentials.
Responsibility remains clear. Lazarus runs the operations and chooses targets. However, exchange and protocol operators still own the duty of care. If an exchange holds massive balances, it must design systems under the assumption of advanced adversaries. That includes minimizing single points of signing failure, using hardened environments for key operations, and enforcing out-of-band verification for high-value withdrawals. It also includes building an incident response plan that can freeze and coordinate quickly because speed matters during laundering.
The scale of Lazarus-linked thefts reached billions across years, and the social impact extends beyond crypto. When state-backed theft funds weapons programs, the harm becomes global rather than local to one exchange. That reality also explains why the policy environment around mixers and laundering infrastructure remains contentious. Some users argue for privacy rights. Authorities argue for disruption of sanctioned activity. ZachXBT’s evidence-focused approach keeps the conversation grounded in observable flows rather than ideology.
The Lazarus exposures also showed the best and worst of crypto transparency. Blockchains preserve the trail. Investigators can follow it. However, criminals can still move quickly, fragment funds, and exploit jurisdictional gaps. Transparency helps attribution and disruption, but it does not guarantee recovery. Therefore, the ecosystem must pair tracing with prevention.
Over time, ZachXBT’s Lazarus work helped normalize a more mature security posture. Teams began treating insider threats, signer compromise, and operational security as primary risks rather than edge cases. Users began understanding that the safest contract still fails when the execution environment fails. That mindset shift matters because it increases the cost of attack and reduces repeat vulnerabilities.
In summary, the Lazarus exposures represent ZachXBT’s role at the frontier where crypto security meets geopolitical conflict. He used on-chain patterns and OSINT to connect attacks into a coherent picture. That work improved attribution, supported disruption efforts, and pushed the industry toward stronger operational controls. Even when it cannot recover every dollar, it changes the playing field by making a powerful adversary visible.
The Solana presale scam wave demonstrated how quickly a legitimate fundraising tactic can turn into a mass exploitation meta. Solana’s ecosystem surged in early 2024 as meme coin launches accelerated. Low fees, fast execution, and viral distribution on social media created an environment where a token could launch, pump, and crash within hours. In that environment, presales became a shortcut for founders and a shortcut for speculators. People sent SOL directly to a wallet in exchange for a promise: the team would later distribute tokens at a better entry price than the public market.
That mechanism removed most safeguards that protect users. If a project uses an on-chain launch contract with transparent distribution logic, users can verify how tokens will be allocated, how liquidity will be seeded, and how vesting will work. In contrast, a direct-wallet presale depends on trust in the recipient. The team can receive funds instantly and still provide nothing. Therefore, the presale meta created a perfect scam format: a single wallet address plus marketing.
ZachXBT published investigations that quantified the scale of the issue. He tracked presale wallets, aggregated inflows, and showed that many projects either abandoned delivery or misused raised SOL. His work mattered because it transformed scattered complaints into a systemic picture. Once users saw that dozens of presales raised massive totals and then disappeared, the community could no longer dismiss the problem as a few bad actors. Instead, it became a pattern of serial fraud.
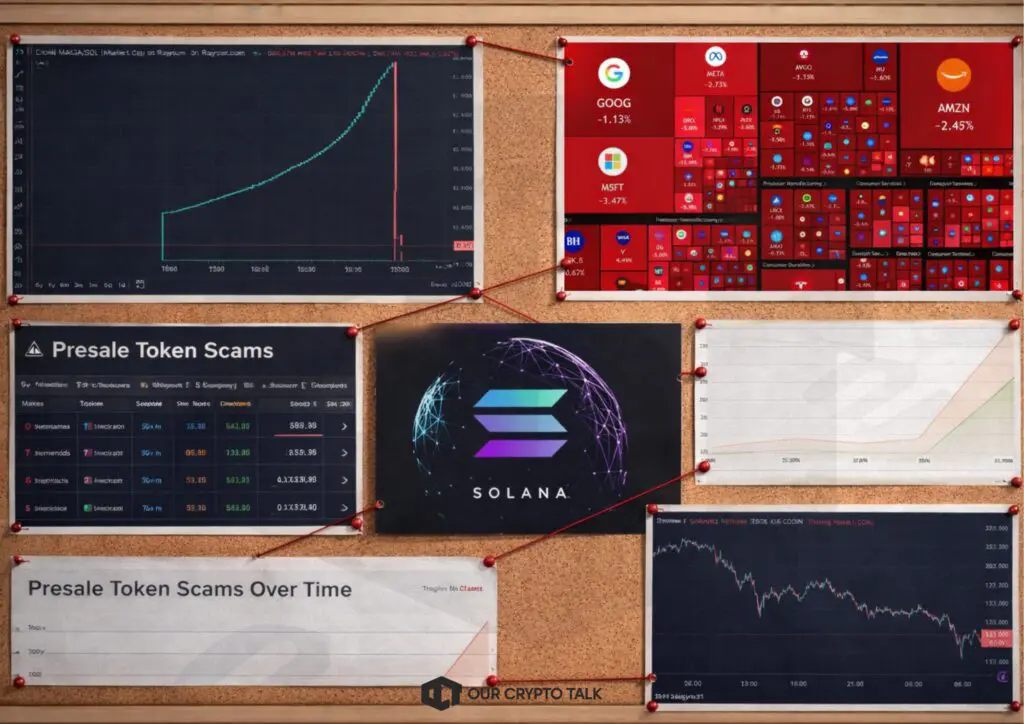
The scam playbook followed a predictable sequence. First, scammers launched a social campaign with aggressive hype. They used influencer partnerships, paid shills, bots, and fake endorsements. Next, they promised early allocation, airdrops, or guaranteed multipliers. Then, they pushed urgency with countdowns and hard caps. Users sent SOL to the presale wallet without any enforceable guarantee. After that, scammers either vanished immediately or executed a partial “delivery” that still functioned as theft. In some cases, they minted a token, provided minimal liquidity, and dumped supply into buyers. In other cases, they never launched at all.
Some scams also combined presales with wallet-draining techniques. Attackers built fake presale sites that requested wallet connection and disguised approvals. Victims who signed the wrong transaction did not only lose the “contribution.” They lost assets across the wallet. That hybrid approach increased the damage per victim and helped scammers extract more than direct SOL transfers.
Responsibility again centered on scammers, but the ecosystem’s incentive structure amplified the success rate. Social platforms reward engagement, and engagement often comes from hype. Influencers profit from promotion. Traders chase high-risk upside. Scammers exploit all three. Solana itself did not “cause” the scams, but the chain’s low friction reduced the cost of launching and the cost of moving proceeds. That frictionless environment benefits innovation and crime equally.
For a crypto reader, the due diligence lesson is straightforward. If a presale asks for direct wallet transfers, treat it as unsecured lending to an anonymous counterparty. If the project does not publish enforceable on-chain distribution rules, you cannot verify that you will receive anything. Even if the team seems credible, the structure still invites abuse because nothing prevents them from keeping the funds.
ZachXBT’s evidence-driven approach also helped the narrative change from “stop being reckless” to “the structure enables fraud.” That distinction matters. Recklessness explains some losses, but structural vulnerability explains why scams scale. When hundreds of millions can flow into presale wallets without escrow, audits, or legal accountability, scammers will keep running the play.
The exposure also sparked more public warnings, including from prominent ecosystem figures, which reduced participation in the most obvious repeats. Over time, users began demanding more transparent launch mechanics, such as locked liquidity, audited contracts, and public vesting schedules. Even meme coin communities started treating presales with more suspicion.
In conclusion, the Solana presale scam wave showed the dark side of speed. The same conditions that allow rapid experimentation also allow rapid theft. ZachXBT revelations made the scale visible with on-chain aggregation and repeated examples. He pushed the community toward healthier norms: avoid direct-to-wallet presales, demand enforceable distribution logic, and treat hype without transparency as a red flag.
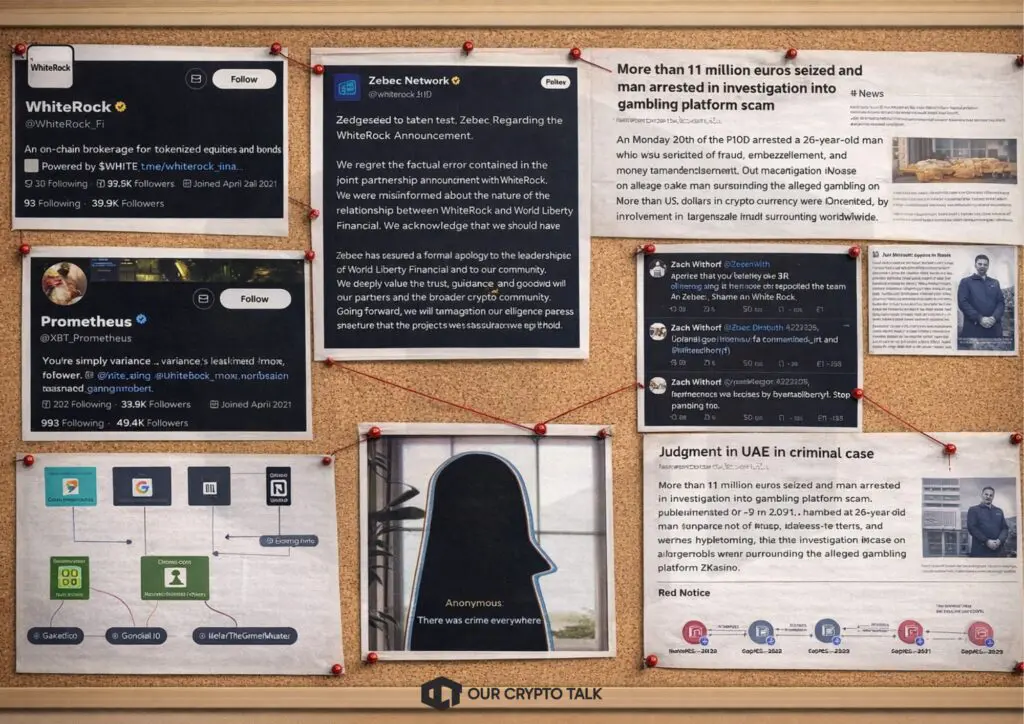
The ZKasino incident became a textbook example of how a “soft rug” can become a hard rug through a bait-and-switch, even when everything appears on-chain. ZKasino marketed itself as a zk-powered gambling platform with big ambitions and aggressive growth tactics. It ran a bridge-to-earn campaign that encouraged users to bridge ETH into the ecosystem with promises of future benefits. The key promise, as widely discussed by the community, involved refunds and favorable terms after launch. Users acted on that promise because they expected a defined redemption path.
ZachXBT revelations exposed a critical shift. The project took bridged ETH and converted it into the project’s token exposure structure rather than returning ETH as many users expected. The team then staked a large portion of ETH through Lido, which extended the lock-up window and reduced the practical ability for users to exit back to ETH. In other words, the project turned deposits into long-duration positions controlled by the team’s decisions. That move generated outrage because it violated the core assumption users relied on when they bridged.
For crypto readers, the important point is custody-like control. Even when a system claims non-custodial execution, bridging campaigns often create escrow behavior. Users send assets into a contract or address that they do not control. They expect to receive something back later based on terms described in a UI, a blog post, or a marketing thread. However, those terms remain off-chain and mutable unless the contract enforces them. If a project controls how and when redemption happens, then the user effectively gives up control during the bridging period.
ZKasino amplified that problem through marketing intensity. It presented itself as a serious product, used strong branding, and leaned on ecosystem hype around zk narratives. Many participants treated the campaign as an opportunity rather than a risk. That is why the eventual shift triggered such broad anger. Users did not only lose value. They lost the ability to unwind the position on their own timeline.
ZachXBT built the case through on-chain forensics and archived proof of prior promises. He traced the bridged ETH flows, identified conversion and staking transactions, and documented the changes in messaging that accompanied the shift. This combination of “what the team said” and “what the wallets did” created a persuasive narrative because readers could verify the chain data themselves. When funds move into staking contracts, the chain produces clear evidence. Therefore, the story did not depend on hearsay.
Responsibility centered on the operators. If a team promises one thing to attract deposits and then changes the terms after the deposits arrive, it acts deceptively. Even if the team frames the change as a “better incentive model,” users do not evaluate incentives after the fact. They evaluate them at decision time. When the team alters the deal after capturing funds, it breaks trust and mirrors classic exit-scam behavior.
The ecosystem also contributed through its typical incentives. Many users chase yield and narrative exposure. Many projects exploit that by designing campaigns that resemble fundraising without calling it fundraising. Bridge-to-earn structures often function as fundraising because they temporarily concentrate liquidity in project-controlled contexts. That concentration creates temptation. It also creates a clear opportunity for a team to delay or deny redemption once it holds enough capital.
ZKasino’s case pushed the community toward stricter norms. Users started demanding that refund logic be enforceable on-chain, not just promised in marketing. They also began treating campaigns that require deposits before clear withdrawals as extremely high risk. Builders learned a reputational lesson too. If a project wants legitimacy, it must hard-code redemption constraints and prove liquidity safety before scaling deposits.
ZachXBT revelations also increased pressure for real enforcement actions when evidence exists. On-chain trails allow investigators to identify where assets moved, what addresses interacted, and how the team executed the shift. That evidence can support legal processes, even if recovery remains difficult. The chain makes the theft visible. However, visibility does not automatically restore funds. It only increases the odds that enforcement can act.
In summary, ZKasino illustrates how DeFi risk often sits above the contract layer. Users face not only code risk but also promise risk. If the rules live in marketing, then the rules can change instantly. ZachXBT forced that lesson into the open by showing the flows and documenting the shift. He reminded the market that the safest assumption remains simple: if you cannot withdraw under on-chain rules you can verify, then you do not control your money.
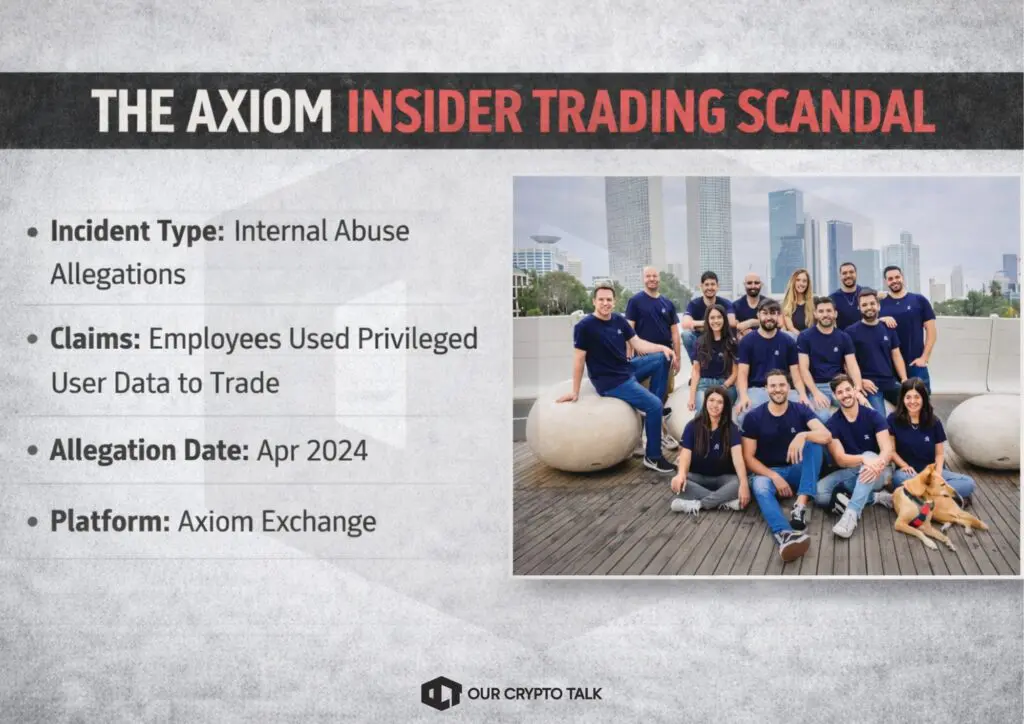
The Axiom insider trading scandal differed from the typical ZachXBT investigation because it focused on internal abuse rather than external theft. In this case, ZachXBT alleged that employees at Axiom Exchange exploited privileged access to user data, then traded based on that information. This allegation struck a nerve because it attacked a core expectation of market fairness. Users can accept volatility. They can accept memecoin chaos. However, they struggle to accept a platform where insiders can see their moves before the market does.
For crypto readers, the structural risk comes from the gap between non-custody and privacy. A platform can let users keep custody of funds while still collecting behavioral intelligence. If the platform offers features like wallet tracking, dashboards, copy trading indicators, or portfolio analytics, it may observe metadata that users do not fully understand. When employees can access that intelligence, they can anticipate large trades, front-run entries, or mirror exits. In thin liquidity conditions, especially on fast-moving Solana memecoin pairs, even small timing advantages can produce substantial gains.
ZachXBT revelations alleged that the abuse involved internal dashboards and tools with excessive permissions. He described a scenario where employees could look up private wallet information or link user identities to wallet behavior. That information would give insiders an informational edge. It could also allow targeted trading strategies. For example, an insider could identify when a high-signal wallet accumulates a token and then buy ahead of the follow-on crowd. Similarly, an insider could sell before the wallet exits and avoid the drawdown.
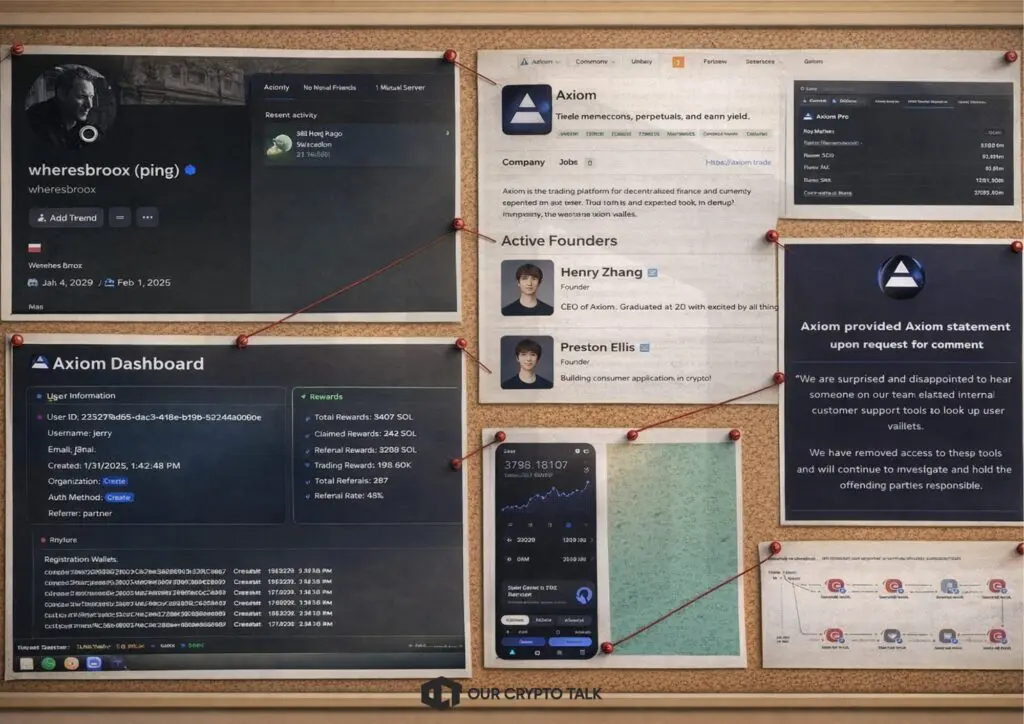
The allegation also highlighted a governance and compliance failure. In traditional finance, firms enforce strict controls around material non-public information. Crypto platforms often scale faster than their governance frameworks. When they prioritize growth, they sometimes deploy internal tools without building mature surveillance and access control systems. That gap creates opportunity for abuse, and it makes abuse hard to disprove because poor logging means poor accountability.
Responsibility, if the allegations are accurate, would fall first on the employees who exploited access for profit. However, it would also fall on leadership for building an environment where such access existed without guardrails. A platform cannot rely on employee ethics alone. It must design controls that make abuse difficult and detectable. That includes least-privilege access, role-based restrictions, immutable audit logs, and real-time alerts for sensitive lookups.
The market impact of insider allegations can exceed the direct profits involved because it hits platform legitimacy. Traders do not only worry about losing funds. They worry about losing edge. If they believe insiders can see their positions, they may leave the platform, reduce volume, and shift liquidity elsewhere. That creates a negative loop. Lower liquidity increases slippage. Higher slippage increases the value of insider timing. Then trust erodes faster.
This story also connected to a wider cultural issue in crypto. Many users treat platforms as tools, not institutions. They assume the platform acts like neutral infrastructure. However, internal dashboards make the platform closer to an intelligence broker. If a platform tracks wallets and monetizes analytics, it sits on information that can distort markets unless it controls access tightly. Therefore, the Axiom allegations acted as a wake-up call. They reminded users that the platform layer can become the adversary even when the chain remains transparent.
ZachXBT’s approach blended digital evidence forms, including alleged internal screenshots, audio references, and on-chain flows that could reflect profit-taking patterns. Even when outsiders cannot fully reconstruct intent without internal logs, public evidence can still expose plausible abuse and force a platform to respond. That pressure matters because it pushes platforms to strengthen controls, publish transparency commitments, and restrict internal access.
In conclusion, the Axiom insider trading scandal underscored a simple reality: market integrity requires governance, not just code. Non-custodial design does not guarantee fair execution if employees can access sensitive user intelligence. ZachXBT revelations shifted attention to the internal threat model that many traders ignore. As crypto infrastructure professionalizes, the industry will need stronger compliance-grade controls around data, access, and employee behavior. Otherwise, the platform layer will keep recreating the same problems traditional finance already learned to police.
ZachXBT’s six landmark revelations, spanning DeFi leadership risk, NFT social engineering, nation-state hacking, presale fundraising fraud, bridge-to-earn deception, and insider data abuse, all point to the same underlying truth: crypto does not eliminate trust. Instead, crypto compresses trust into new choke points, such as treasury roles, Discord permissions, internal dashboards, and liquidity mechanics.
In Wonderland, the community learned that treasury control equals power, so identity and governance transparency matter. BAYC phishing, users learned that attackers steal signatures, not passwords, and that community infrastructure can become a criminal distribution channel.In Lazarus-linked hacks, the industry learned that the adversary often acts like a nation-state, so security must protect organizations as much as contracts. Solana presale scams, traders learned that direct-to-wallet fundraising often removes every safeguard that protects users.In ZKasino, deposit campaigns taught users to demand on-chain redemption guarantees instead of trusting websites and timelines. Finally, in Axiom’s insider trading allegations, the community saw that non-custodial execution does not remove privacy and fairness risks when employees can access sensitive user intelligence.
Across all six stories, ZachXBT revelations shows why on-chain transparency remains powerful. The chain records the flows. However, investigators still need to interpret the flows, connect clusters, and push narratives into the public sphere until action follows. That persistence deters scammers, educates users, and raises the cost of abuse in an ecosystem that too often rewards speed over controls.


Top 6 ZachXBT Revelations That Shocked The World
AI Agent Payments Explained: Circle Nanopayments and the x402 Protocol
Top 7 Projects in the World Liberty Financial (WLFI) Portfolio
Where Crypto Actually Makes Money in 2026?
Top 6 ZachXBT Revelations That Shocked The World
AI Agent Payments Explained: Circle Nanopayments and the x402 Protocol
Top 7 Projects in the World Liberty Financial (WLFI) Portfolio
Where Crypto Actually Makes Money in 2026?